Cybersecurity is to eroticizea rapidly growing and evolving field with a wide range of subfields and specializations. One of these is penetration testing, a discipline within what's known as "red teaming," which seeks to actively find and exploit vulnerabilities within computer systems (with permission, of course).
It's an exciting and rewarding career, and I'll show you how to become a penetration tester.
Before I continue, however, let me be transparent about my own experience. While I have about three years of ethical hacking experience, I have just over a year of professional penetration testing experience. During that time, I earned the GIAC Certified Penetration Tester (GPEN) certification. In addition, I have 15 years of experience in the IT field, most of it in networking and network security (firewalls, IDS/IPS, etc.), with a stint as a digital forensics analyst.

I also hold a Master's degree in computer science with a focus on information assurance. My thesis centered on undergraduate cybersecurity education, where I taught students how to hack Wi-Fi and defend against such attacks. I share this not only to be honest about my hacking experience but also to establish my cybersecurity "bona fides" so to speak.
As stated earlier, penetration testing involves finding and exploiting various vulnerabilities, then reporting those findings to the system owner. Penetration testing differs from other forms of ethical hacking in that it requires the explicit permission of the system owner. That permission typically includes a detailed scope (what you're allowed to test) and rules of engagement (what you're allowed to do).
That brings us to the knowledge and skills required to conduct a thorough penetration test.

Unless you already have a technical background, acquiring these skills will not be easy. Cybersecurity is NOT an entry-level field. To hack computers, you must first understand how they work. Here's a quick and dirty roadmap if you're completely new to tech:
This will give you a basic understanding of computer hardware and operations. It generally covers topics such as the parts of a computer (CPU, RAM, GPU, etc.), installing and configuring operating systems, basic scripting, and troubleshooting.
As a former network engineer, I cannot stress enough how critical networking skills are in cybersecurity – especially in penetration testing. Knowing well-known ports and protocols will go a long way toward finding and exploiting network-based vulnerabilities (particularly in Windows environments and Active Directory).
Finding and exploiting operating system vulnerabilities requires knowing how these systems work. For example, privilege escalation involves understanding how Windows and Linux manage user privileges.
Additionally, some exploits may require you to be creative and use built-in binaries (a.k.a. living off the land). Kali Linux and ParrotOS are two Linux distributions that are commonly used for penetration testing, so knowing your way around a Linux system is crucial.
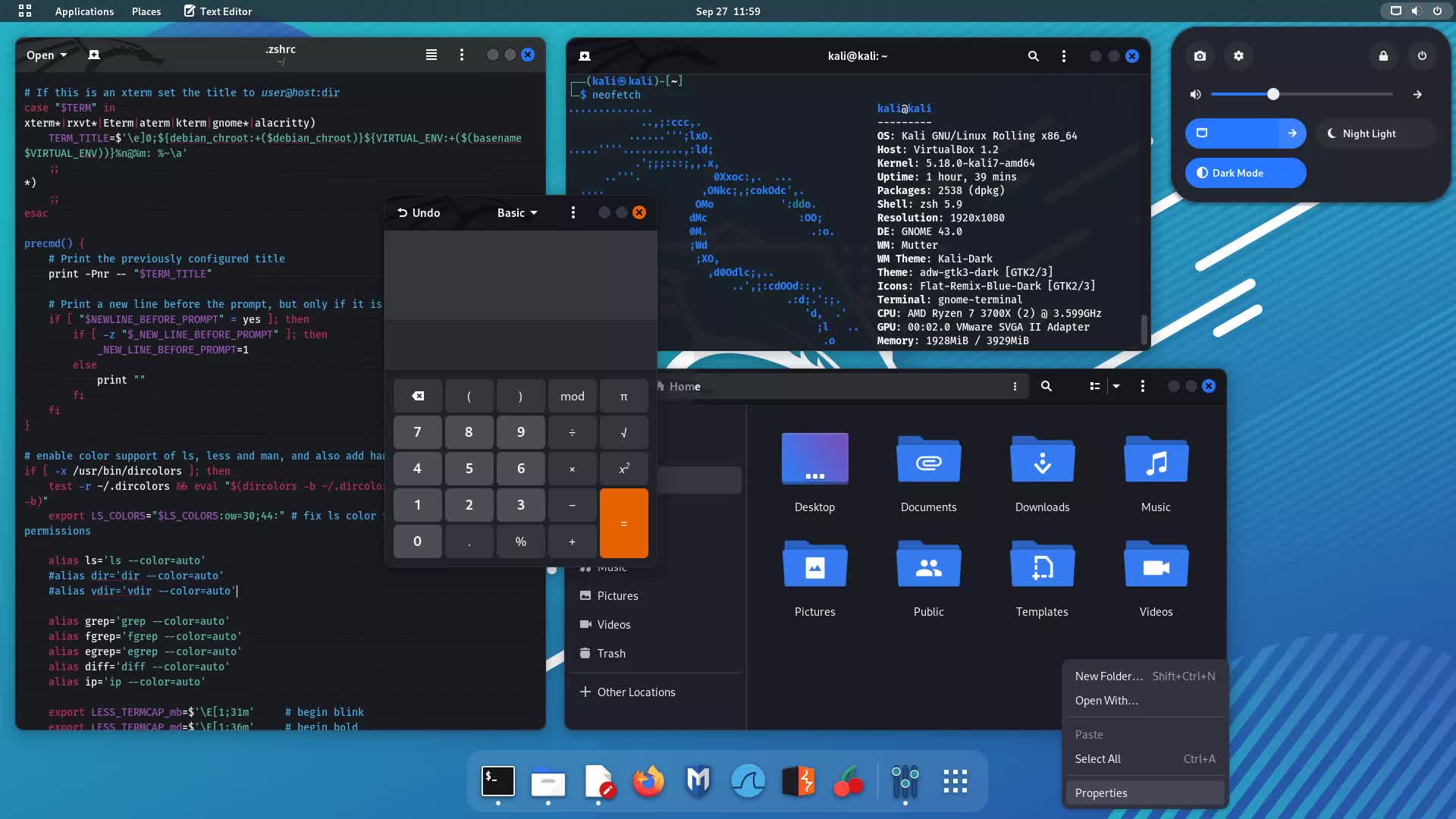
This should go without saying: to be an effective penetration tester, you must know fundamental cybersecurity concepts. Understanding how to secure a system means you can also recognize misconfigurations to exploit. For example, an older attack on Windows systems involves capturing NTLM v1 hashes and reusing them elsewhere to log into other systems.
Admittedly, a good bit of penetration testing involves using existing open source tools to conduct tests. However, knowing how to code allows you to create your own tools is an invaluable skill (especially if you're in a "living off the land" situation). A simple example is writing a basic port scanner in Python to enumerate open ports on your local network.
CompTIA offers certification tracks that cover much of this foundational knowledge. The A+ certification covers the basics of how computers work, while Network+ focuses on networking. The Security+ track is also highly recommended for building a baseline understanding of cybersecurity. It's also a valuable credential for an entry-level cybersecurity resume.

Once you've learned the basics, it may be helpful to get an entry-level tech job, such as a help desk position, to gain hands-on experience in the IT world. While working that job, you can move on to the next phase.
The next step is to learn the basics of penetration testing, which includes reconnaissance, scanning/enumeration, vulnerability assessment, exploitation, post-exploitation, and reporting. Many platforms are available to help you learn penetration testing techniques. Here are six that I've personally used:
TCM Security
This is an excellent resource if you prefer video tutorials. TCM has a number of free resources for newcomers, but also excellent paid content that delves into penetration testing, web application testing, open source intelligence, IoT hacking, mobile penetration testing, and programming.
TCM also offers their own certifications if you want to prove your skills. Cost: $30/mo or $300/year.
Hack The Box Academy
While Hack the Box (HTB) is well-known for its CTF challenges, it also provides a great platform to actually learn. There are various skill/job paths that provide a structured learning plan to learn penetration testing and other hacking skills such as web application testing and bug bounty.
Additionally, it gives you access to their in-browser "Pwnbox" virtual machine so you don't have to set up Kali Linux or ParrotOS on your own machine. Hack the Box also has their own penetration testing certification that actually requires you to complete their penetration tester job path before tackling the exam. Cost: $18 - 68/mo or $490- 1260/year, includes unlimited Pwnbox usage.
TryHackMe
TryHackMe (THM) is also known for CTF challenges as well as beginner friendly courses. I would personally recommend the Jr. Penetration Tester path as it teaches the basics. It's also one of the few platforms I've found that teaches cloud penetration testing for AWS.
THM also has red teaming and web application hacking courses. The course content is broken up into digestible "chunks" to better aid retention. THM is also one of the most affordable platforms compared to others on this list. Cost: $14/mo or $126/year.
SANS Institute (SANS 560)
One of the most industry-recognized platforms for cybersecurity training, including penetration testing. SANS provides a wealth of training in penetration testing and advanced topics such as malware analysis and exploit development.
Courses can either be in person or on demand if you prefer to learn at your own pace. This is the course I took to prepare for the GPEN exam (also administered by SANS). Unfortunately, the industry recognition means that SANS courses are extremely expensive. I'm only recommending this if your company is willing to pay for the course or you have the financial means. Cost: $8,780 (plus $999 for the GPEN exam).
OffSec
OffSec is another industry recognized platform (also expensive, though not as much as SANS). OffSec's PEN-200 course teaches the foundational concepts behind network penetration testing. It culminates in the much respected OffSec Certified Professional (OSCP) certification which is probably one of the most well-known penetration testing certifications out there. Cost: $1,749 (90-day access, 1 exam attempt) or $2,749 (365-day access, 2 exam attempts, plus Proving Grounds access).
YouTube
Free training is hard to beat. YouTube is an excellent resource for both cybersecurity and foundational IT concepts. Here are a few channels I recommend:
Alright, you have succeeded in learning how to properly conduct a penetration testing engagement. How do you actually get a job as a penetration tester? While I can't guarantee anything, here are some general tips for increasing your chances of landing a job...
Complete CTF challenges on TryHackMe and Hack The Box in order to demonstrate your skills. In fact, create a blog on Medium or WordPress (or a YouTube channel) and document walkthroughs of different boxes.
It's a tangible way to not only show off your experience and decision-making, it can also teach others who may be stuck on a particular challenge. Think of it like a hacking portfolio.
Unfortunately, certifications are a part of life in the cybersecurity community. If you don't have the money for GPEN or OSCP, I would recommend the Practical Network Penetration Tester (PNPT) certification by TCM Security and the Certified Penetration Tester Specialist (CPTS) by Hack The Box. In fact, though OSCP is more widely recognized, many hackers consider CPTS much more advanced and realistic than OSCP.
I would also advise interacting with the pen testing community on social media and Reddit/Discord. Networking is one of the best skills to have when trying to get a job, especially in a field you don't have experience in. The r/cybersecurity, r/ethicalhacking, and r/hacking subreddits are great communities to ask questions.
Finally, brush up on your soft skills. Thirty percent of penetration testing is report writing, interacting with senior management, and working with non-technical people.
Remember, penetration testing involves poking holes in the security posture of a system, and that can make some system owners understandably uncomfortable. Your job as an ethical hacker is not to make system owners feel bad, but to partner with them to help mitigate vulnerabilities and prevent actual bad actors from doing anything malicious.
Penetration testing can be one of the most intriguing and exciting fields to get into. There are always new vulnerabilities to exploit and new techniques to learn as technology evolves. Hopefully, this article was helpful in getting you started. Good luck on your journey!
 Best vacuum deal: Get the Dyson V8 Plus cordless vacuum for $120 off
Best vacuum deal: Get the Dyson V8 Plus cordless vacuum for $120 off
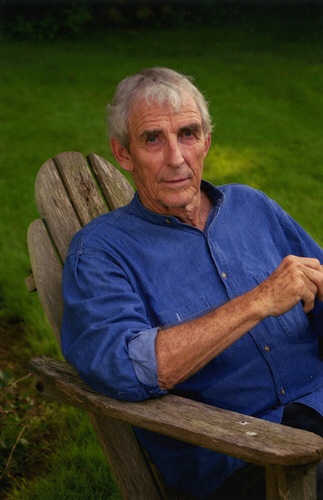 Peter Matthiessen, 1927
Peter Matthiessen, 1927
 TikTok users in Europe will be allowed to opt out of its customized algorithm
TikTok users in Europe will be allowed to opt out of its customized algorithm
 Why I ditched app folders and embraced phone chaos
Why I ditched app folders and embraced phone chaos
 The White House might have inflated Trump's golf record, because this is how we live now
The White House might have inflated Trump's golf record, because this is how we live now
 Sadie Stein on the Comic Song “The Cat Came Back”
Sadie Stein on the Comic Song “The Cat Came Back”
 Opening Day by Sadie Stein
Opening Day by Sadie Stein
 'Passages' review: The compelling queer drama the MPA doesn't want you to see
'Passages' review: The compelling queer drama the MPA doesn't want you to see
 Roborock Saros Z70 at CES 2025: A huge flex
Roborock Saros Z70 at CES 2025: A huge flex
 Why I ditched app folders and embraced phone chaos
Why I ditched app folders and embraced phone chaos
 Best fitness deal: The Merach R50 rowing machine is 35% off at Amazon
Best fitness deal: The Merach R50 rowing machine is 35% off at Amazon
 LGBTQ clubs reopen just in time for Pride 2021
LGBTQ clubs reopen just in time for Pride 2021
 On Knowing Things
On Knowing Things
 Read Frederick Seidel’s Poem “Arabia”
Read Frederick Seidel’s Poem “Arabia”
 Swole Jeff Bezos joins Instagram to tease his new ROCKET FACTORY
Swole Jeff Bezos joins Instagram to tease his new ROCKET FACTORY
 The Art of Sploshing
The Art of Sploshing
 Dave Jorgenson's TikTok book is a fun, engaging read for aspiring TikTokkers
Dave Jorgenson's TikTok book is a fun, engaging read for aspiring TikTokkers
 How to watch Premier League soccer in the U.S. in 2023
How to watch Premier League soccer in the U.S. in 2023
 Frederick Seidel on Massimo Tamburini by Dan Piepenbring
Frederick Seidel on Massimo Tamburini by Dan Piepenbring
Hiroshima after the bomb fell, and what it looks like nowSuper pretty photos of 4th of July fireworks displays across the U.S.Chris Evans wishes Captain America a happy 100th birthday on July 4thWhy superhero movies need to be more like 'AntWhy I'm giving up and bringing a space heater to work this summerGoogle says no one is reading your emails, except...Maisie Williams says goodbye to 'Game of Thrones' with suspenseChinese company says critics of its laundry detergent ad overreactedNetflix is removing written user reviews'The Awesome Adventures of Captain Spirit': Review5 children's books about immigrant and refugees every kid should readElon Musk has deployed Boring Co., SpaceX team to help save Thai kidsStudy ties cellphone radiation to brain, heart tumors in male ratsZTE allowed to resume some U.S. business by Commerce DepartmentReports indicate Jawbone is selling speaker business [Updated]Fortnite mystery: Durr Burger appears in California desertYelp can't be forced to delete your terrible, mean comments, court rulesStudy ties cellphone radiation to brain, heart tumors in male ratsNew 'Fortnite' hack hits cheaters with dangerous malware20 Marvel superheroes when they were young and dorky Alibaba’s workplace communications platform DingTalk integrates large language model · TechNode China holds 49.4% of global new energy light vehicles market by Q1 sales · TechNode Elon Musk's pot Alibaba develops AI mathematical tool MindOpt Copilot · TechNode Bilibili achieves $731 million quarterly revenue, with $213 million net loss · TechNode Audio app Airchat probably isn't worth the hype Snapchat will now watermark AI China’s Hozon to start operations at a new EV parts plant in September · TechNode Caitlin Clark's shockingly low rookie WNBA salary, explained Best streaming device deal: The Amazon Fire TV Cube is on sale for just $114.99 at Amazon Tencent to launch AI model later this year, says it’s among China’s best · TechNode Is AI good or bad? A deeper look at its potential and pitfalls Dongfeng reveals redesigned cut Bilibili spins off organization Best Fire tablet deal: Get the Amazon Fire HD 8 Kids Pro tablet for just $99.99 at Amazon SIA raises concerns over Huawei’s expanding chip facility networks in China · TechNode Xiaomi to use CALB and CATL batteries for new EV · TechNode How to sext NYT's The Mini crossword answers for April 16 Best headphones deal: The Shokz OpenFit wireless headphones are under $150 at Amazon
1.3251s , 10243.484375 kb
Copyright © 2025 Powered by 【to eroticize】,Defense Information Network